15 Security Tips for Linux VPS Hosting
 Virtual Private Servers (VPS) give website owners more control of their site’s configurations and experience, so it’s no surprise that most website owners prefer it over standard shared hosting. Since customers have more control over server settings, VPS service is more challenging to secure. It’s still a virtual server connected to the network, so security for host administrators and customers should be a priority to protect data on the VPS instance and the host network. The articles covers the following topics related to Linux VPS security:
Virtual Private Servers (VPS) give website owners more control of their site’s configurations and experience, so it’s no surprise that most website owners prefer it over standard shared hosting. Since customers have more control over server settings, VPS service is more challenging to secure. It’s still a virtual server connected to the network, so security for host administrators and customers should be a priority to protect data on the VPS instance and the host network. The articles covers the following topics related to Linux VPS security:
Top 10 Web Hosting Security Best Practices

The internet contains over 1.7 billion websites, and every one of them is hosted by at least one web server. A web server can host hundreds of sites on one physical machine, but depending on the way it’s hosted, just one hacked website can be the downfall for all sites on the server. Security for web hosters is more important than ever as more customers depend on your cybersecurity best practices and monitoring to find ongoing attacks. Web servers usually host several business sites, which store customer data, so they are common targets for attackers. So, we've put together a list of hosting security best practices and tips essential for web hosting security. This articles covers the following hosting security topics:
Server Security Best Practices: 10 Tips to Protect from Cyber Attacks

A system administrator (or sysadmin) is perhaps one of the most stressful careers available to an aspiring computer science and information technology student. Sysadmins are typically responsible for network and computer systems, including but not limited to server security. A sysadmin’s job, therefore, is stressful because at any time an organization’s servers may fall victim to cyber attacks.
18 Ways to Improve cPanel Security
The introduction of cPanel in 1996 simplified Linux hosting management, and almost 30 years later it’s still a favorite for website owners and hosters alike. The changes in the Linux operating system, additional distributions, new attack vectors, and discovered vulnerabilities force cPanel developers to release security patches frequently. The cPanel software has gone through several version updates, and each change increases complexity. The added complexity makes it more likely for hackers to find vulnerabilities, but your business can reduce risks by following these best practices to avoid becoming a victim of an exploit. The article goes over tips and tricks on how to keep your cPanel account protected.
What are Antivirus False Positives and What to Do About Them?

False positives from your monitoring applications can cause undue stress and unnecessary overhead for administrators if they do not have the security knowledge to identify them. If monitoring software reports inaccurate information, administrators unfamiliar with cybersecurity could make changes based on the application’s false positives that could harm the security and stability of the environment.
WordPress Security Fundamentals: Ultimate Guide 2023

The WordPress content management system or (CMS) is one of the most popular web applications on the market. It’s estimated that WordPress powers almost 43% of the internet, up from 30% just a few years ago. The foundation for the content management system’s success is its convenience, simple installation, and vast theme and plugin community. WordPress can be used by someone who has very little knowledge of the ways a web application functions, but it comes at the expense of security. The article covers the following topics:
Important Vulnerability on Advanced Custom Fields Plugin for WordPress
The recent cyber attack found by Patchstack researcher Rafie Muhammad on the "Advanced Custom Fields" plugin for WordPress is a stark reminder of how vulnerable websites can be to hackers. In this case, over two million users were at risk of cyberattacks due to a vulnerability (a flaw, tracked as CVE-2023-30777) that allowed miscreants to inject malicious code into webpages and potentially hijack administrative accounts.
Fortifying Server Security: Unveiling the Significance of Apple's Recent Security Update

With Apple’s recent release of a security update for the iPhone, iPad, and Mac, it brings attention to the critical importance of regular software updates. We’re going to explore the significance of staying up-to-date with the latest security patches and highlight the efforts of Imunify360 in enhancing their update process to deliver faster and safer protection for servers.
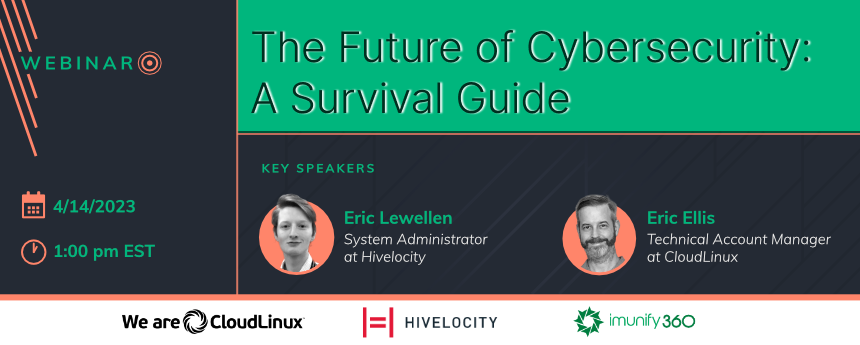
[New Video Content] “The Future of Cybersecurity: A Survival Guide”
Welcome to the video recording of our interactive webinar on server security. CloudLinux Technical Account Manager Eric Ellis and Hivelocity Sr System Admin Eric Lewellen provide an overview of common server security ideas and engage in a lively debate about which ones matter and which ones don't.
[New Webinar] "The Future of Cybersecurity: A Survival Guide"
Companies are increasingly at risk for security breaches in 2023. We’ve seen hacks at some of the biggest companies recently – LastPast, and GoDaddy (to name a few). Join CloudLinux Technical Account Manager Eric Ellis and Hivelocity System Admin Eric Lewellen for an overview and some lively debate about some of the most common server security ideas – which ones matter and which ones don’t.

 6 Layers of Protection
6 Layers of Protection







.jpg?width=769&height=433&name=webinarcover_YT_R01%20(1).jpg)




.png?width=115&height=115&name=pci-dss%20(1).png)
